Multi-Factor Authentication (MFA): Boost Security While Keeping Access Simple
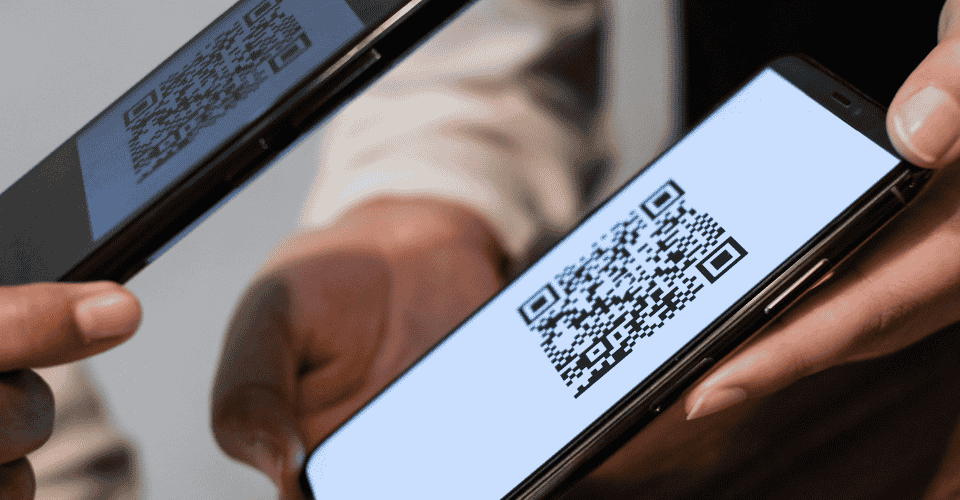
In today’s digital world, protecting your business goes far beyond strong passwords. Multi-Factor Authentication (MFA) locks down access by requiring users to confirm their identity in more than one way, such as a password plus a verification code or a biometric check. This simple addition creates a powerful line of defence against cybercriminals. MFA isn’t just “extra steps.” It’s a practical, proven way to stop the vast majority of breach attempts — even if attackers already have a password. By adding another layer of verification, you make it much harder for unauthorised people to reach sensitive systems and data.
Why MFA Matters for Your Business
Passwords alone are no longer enough. Most breaches today occur because weak or stolen credentials are used to gain access, and they happen fast. Multi-Factor Authentication helps change that by requiring two or more verification methods before granting access. Here’s what MFA protects against:
- Credential theft and phishing — Where stolen passwords are used to log in.
- Automated attacks — Bots trying common username/password combinations.
- Unauthorised remote access — Especially critical for hybrid or remote workforces.
According to industry research, MFA can block more than 99% of account compromise attacks, making it one of the most effective ways to secure your business. Security doesn’t have to be hostile or slow; modern MFA is designed to be smooth for your team while blocking threats before they escalate.